Friday Roundup - Week 15: Mythos, Malware, and a Moon Return
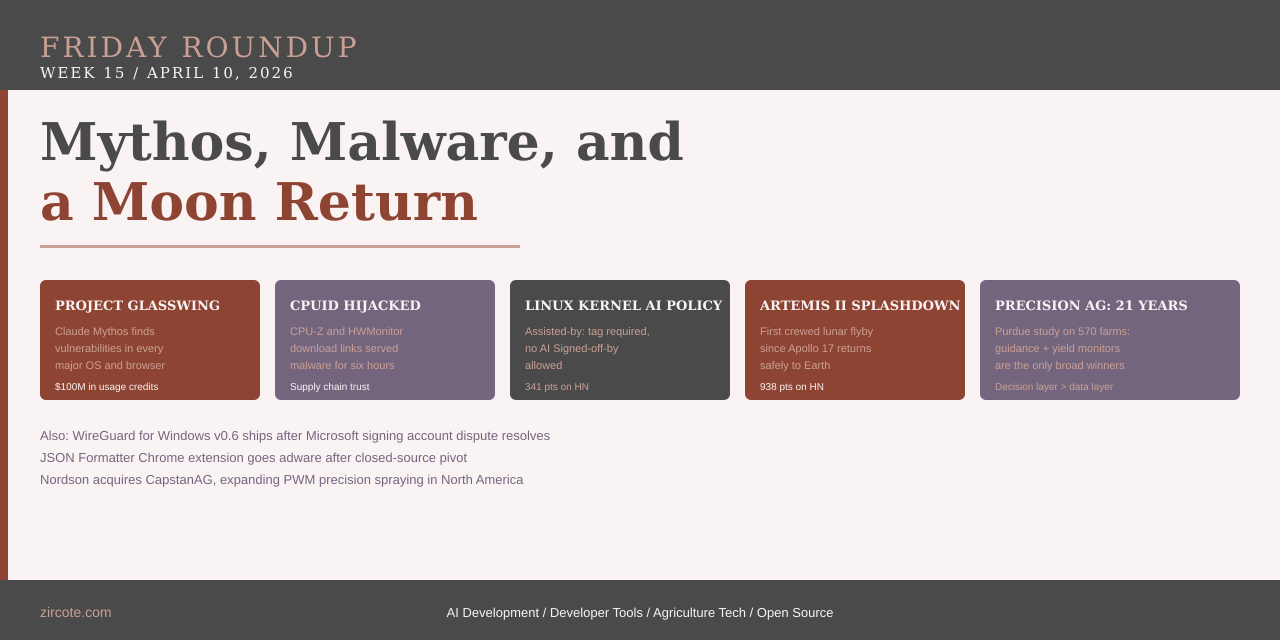
The biggest story of the week landed Monday morning before most developers had opened a pull request. Anthropic announced Project Glasswing: a coalition of twelve major technology organizations, a $100M commitment in model usage credits, and a new frontier model that can find vulnerabilities in every major operating system and web browser. The defensive framing is credible. The underlying capability described is not abstract.
The rest of the week confirmed that the threat model behind Glasswing is not hypothetical. CPUID’s website served malicious downloads for six hours. A widely-installed Chrome extension injected adware after going closed-source. Two stories, same root cause: trust delegated to a name without verification of what that name points to at any given moment.
Project Glasswing: AI Finds Vulnerabilities in Every Major OS and Browser
On April 7, Anthropic published details on Project Glasswing, a new initiative built around a previously unannounced model called Claude Mythos Preview. The launch partners include AWS, Apple, Broadcom, Cisco, CrowdStrike, Google, JPMorganChase, the Linux Foundation, Microsoft, NVIDIA, and Palo Alto Networks.
The technical claim at the center of Glasswing is specific: Mythos Preview has already identified thousands of high-severity vulnerabilities, including some in every major operating system and web browser. Anthropic’s reasoning for the coalition structure follows from that claim. If a model at this capability level exists inside one lab, similar capabilities will proliferate. The choice is whether those capabilities are deployed offensively or defensively first.
The concrete commitments: Anthropic is providing up to $100M in Mythos Preview usage credits across the twelve launch partners, extending access to over 40 additional organizations that maintain critical software infrastructure, and donating $4M directly to open-source security organizations. Partners will use the model as part of their existing defensive security workflows and share findings back to the broader initiative.
The strategic positioning matters separately from the security framing. Glasswing demonstrates a capability at a moment when the supply chain attack stories from Week 14 (the TeamPCP Trivy-to-Axios lateral chain) are still in the news cycle. A model that can scan your entire codebase for exploitable vulnerabilities before a threat actor does is a compelling product regardless of the coalition wrapper around it.
For teams maintaining public-facing infrastructure: the 40-organization access program for open-source maintainers is worth investigating. Anthropic has not published the application process publicly yet, but the Linux Foundation’s participation in the coalition suggests the intent to reach critical open-source projects.
CPUID: Six Hours, Malicious Downloads, 339 Points on HN
On April 9 and 10, CPUID’s download infrastructure served modified installers for HWMonitor and CPU-Z. Users began reporting that installers tripped antivirus alerts or downloaded files with unexpected names. One circulating example showed HWMonitor pointing to HWiNFO_Monitor_Setup.exe, a name designed to blend into a legitimate update workflow.
CPUID confirmed the breach: a secondary API was compromised for approximately six hours, causing the main site to serve malicious download links. The signed binaries themselves were not modified. The attack sat in the delivery layer, not the build layer.
The vx-underground analysis of captured samples shows the malicious installer targeted 64-bit HWMonitor users, delivered a fake CRYPTBASE.dll, and reached out to a C2 server to pull additional payloads. The attack ran largely in-memory using PowerShell, compiled a .NET payload on the victim machine, injected it into other processes, and went after browser credential stores through Chrome’s IElevation COM interface. Infrastructure overlap with earlier FileZilla-targeting campaigns suggests a consistent threat actor operating across multiple software distribution channels.
The distinction CPUID is drawing, that the signed binaries were clean while only the download links were swapped, is technically accurate and operationally irrelevant to anyone who clicked a download link during those six hours. The installer you ran was not the one the signature covers. The HN thread (339 points, 92 comments) noted this plainly: download link integrity requires the same verification rigor as code signing, and almost no users apply it.
The mitigation is the same one that comes out of every supply chain story: verify hashes before executing anything you download. CPUID publishes SHA-256 hashes alongside installers on their downloads page. Those hashes are served from the same compromised infrastructure during an active attack, which makes out-of-band verification (a reference hash from a prior known-good download, or a hash published on a separate channel) the only reliable check.
JSON Formatter: From Open Source to Adware
A separate story with 226 HN points this week: a widely-installed Chrome extension that formats JSON in browser windows moved to a closed-source model and began injecting adware. The original developer had archived the public repository and launched a commercial version. The commercial version’s behavior was not disclosed to existing users.
The pattern is familiar in extension ecosystems. Extensions accumulate install base under an open-source model. The developer monetizes by selling the extension, changing its behavior, or both. Users who installed for one set of behaviors get different ones on the next update, automatically, with no review step.
The practical response is the one the HN thread converged on: browser extension permissions are a persistent trust delegation, not a one-time installation decision. An extension with access to page content on all URLs has that access on every update. For extensions handling developer workflows (JSON formatting, API inspection, auth token display), the risk profile is high enough that pinning extension versions or using a fork with a fixed source commit is worth the maintenance overhead. The developer’s response was to publish the original codebase as “JSON Formatter Classic” in the Chrome Web Store for users who want the open-source version without commercial behavior.
Linux Kernel Formalizes AI Contributor Policy
The Linux kernel’s documentation tree gained a new file this week: Documentation/process/coding-assistants.rst. The HN thread (341 points, 252 comments) described it as “refreshingly normal” and then immediately argued about it for 252 comments.
The substantive policy is two rules. First, AI agents must not add Signed-off-by tags. The Developer Certificate of Origin requires a human to certify the contribution, and that certification cannot be delegated to a tool. Second, contributions should include an Assisted-by: tag in the format Assisted-by: AGENT_NAME:MODEL_VERSION [TOOL1] [TOOL2] to attribute which tools participated.
The comment thread surfaced the real tension: not the policy itself, but the enforcement gap between stating acceptable behavior and detecting violations. A Signed-off-by tag from a human who did not actually review AI-generated code is indistinguishable from any other Signed-off-by tag. The policy puts responsibility where it belongs (the human submitter is responsible for review, license compliance, and the DCO certification) but does not create a new detection mechanism. What it does create is a clear standard against which maintainers can reject contributions where review evidence is absent and AI generation is apparent.
For teams using Claude Code, GitHub Copilot, or similar tools on contributions to kernel-adjacent projects: check whether your target project has a similar policy, and document your review process explicitly when you submit. The attribution expectation is spreading.
WireGuard for Windows v0.6 Released
WireGuard for Windows v0.6 shipped Friday, the first significant Windows release in a long time. Jason Donenfeld’s announcement covered the technical improvements (individual allowed IP removal without packet drops, low MTU support on IPv4, toolchain updates across the EWDK, Clang/LLVM/MinGW, and Go versions) and also addressed the Microsoft account suspension story that circulated earlier this week.
The short version: Microsoft suspended the signing account required to ship the updated Windows kernel driver. Donenfeld posted about it in a Hacker News comment, the discussion reached Microsoft, and the account was restored the same day. The release followed shortly after. His characterization was direct: “I think this is just a case of bureaucratic processes getting a bit out of hand, which Microsoft was able to easily remedy.”
The technical highlight from the release notes is the minimum supported Windows version change. WireGuardNT and WireGuard for Windows have dropped legacy compatibility codepaths that accumulated over years of supporting very old Windows versions. The resulting codebase is smaller, the dynamic dispatch paths are gone, and the driver builds on a more current EWDK. For organizations still running WireGuard VPN infrastructure on Windows: the update is a straightforward security and performance improvement.
Artemis II Splashes Down
Artemis II returned safely on Friday with four crew members after a successful lunar flyby, the first crewed mission to leave Earth orbit since Apollo 17 in 1972. The HN thread reached 938 points and 289 comments, the highest-scored story on the site this week.
The mission demonstrated lunar transit capability, deep space communication at distance, and life support systems under actual flight conditions rather than simulation. For a program that has taken years longer and cost more than planned, a successful crewed mission is the result that validates continued investment in the architecture.
Agriculture: What 21 Years of Precision Ag Data Actually Shows
Purdue University published a 21-year study covering 570 Kansas farms from 2002 to 2022, analyzing whether precision agriculture technology improves farm efficiency as measured by the ability to generate gross revenue while minimizing costs.
The headline finding is the kind that gets quoted selectively: on average, precision agriculture technology does not broadly improve farm efficiency. Across seventeen technology combinations studied, most were not associated with meaningful gains. The added cost of adoption was not offset by higher revenue.
Two exceptions hold up under the analysis. Automated guidance improves efficiency consistently. The combination of yield monitors with grid soil sampling also shows gains, but only after a learning period, because the data those tools generate requires the farmer to act on it. The researchers describe this as a “catch-up effect” rather than a general return on investment. Less efficient farms see the most benefit from several technology combinations. Highly efficient farms see little to none.
The finding is more nuanced than either the “precision ag always pays” or “precision ag is oversold” narratives. The technologies that pay are the ones that either remove a specific labor cost (guidance) or generate information that experienced operators can act on (yield monitors combined with grid soil sampling). Technologies that generate data without a clear decision workflow behind them do not show efficiency gains in this dataset.
For sheep producers applying this to NSIP genetic data or IoT sensor infrastructure: the Purdue finding reinforces the pattern. The data layer matters less than the decision layer. Genetic EBV data from NSIP is highly predictive. A tool that surfaces that data at the moment a purchasing decision happens is where the value gets realized, not in the data collection itself.
Separately, Nordson Precision Agriculture announced the acquisition of CapstanAG, the Topeka, Kansas company that pioneered pulse width modulation technology for nozzle-by-nozzle spray control. CapstanAG’s PWM systems reduce herbicide application and improve placement accuracy for row crops, orchards, seeding, and aerial application. The acquisition expands Nordson’s ARAG product line into the North American market with a company that has direct customer relationships across leading manufacturers and operators.
Links
Security
- Project Glasswing: Securing Critical Software with AI - Anthropic
- CPU-Z and HWMonitor compromised - The Register
- JSON formatter Chrome plugin now closed and injecting adware - GitHub (HN, 226 pts)
Developer Tools
- AI assistance when contributing to the Linux kernel - kernel.org (HN, 341 pts)
- WireGuardNT v0.11 and WireGuard for Windows v0.6 Released - Jason Donenfeld (HN, 484 pts)
Space
- Artemis II safely splashes down - CBS News (HN, 938 pts)
Agriculture Tech
- Purdue Measures Precision Payoffs on 570 Farms in 21 Years - Precision Farming Dealer
- Nordson Acquires CapstanAG - Precision Farming Dealer
Follow @zircote for weekly roundups and deep dives on AI development, developer tools and agriculture tech.